Activity Log
Monitor all user actions and system events in a comprehensive audit trail. The Activity Log helps you track changes, ensure accountability, troubleshoot issues, and maintain security.
-
What is Activity Log?
: Audit trail
- • Definition : Comprehensive record of all user actions and system events
- • Purpose : Track changes, audit user behavior, troubleshoot issues, ensure compliance
- • Visibility : See who did what, when, and where
- • Security : Detect unauthorized access or suspicious activity
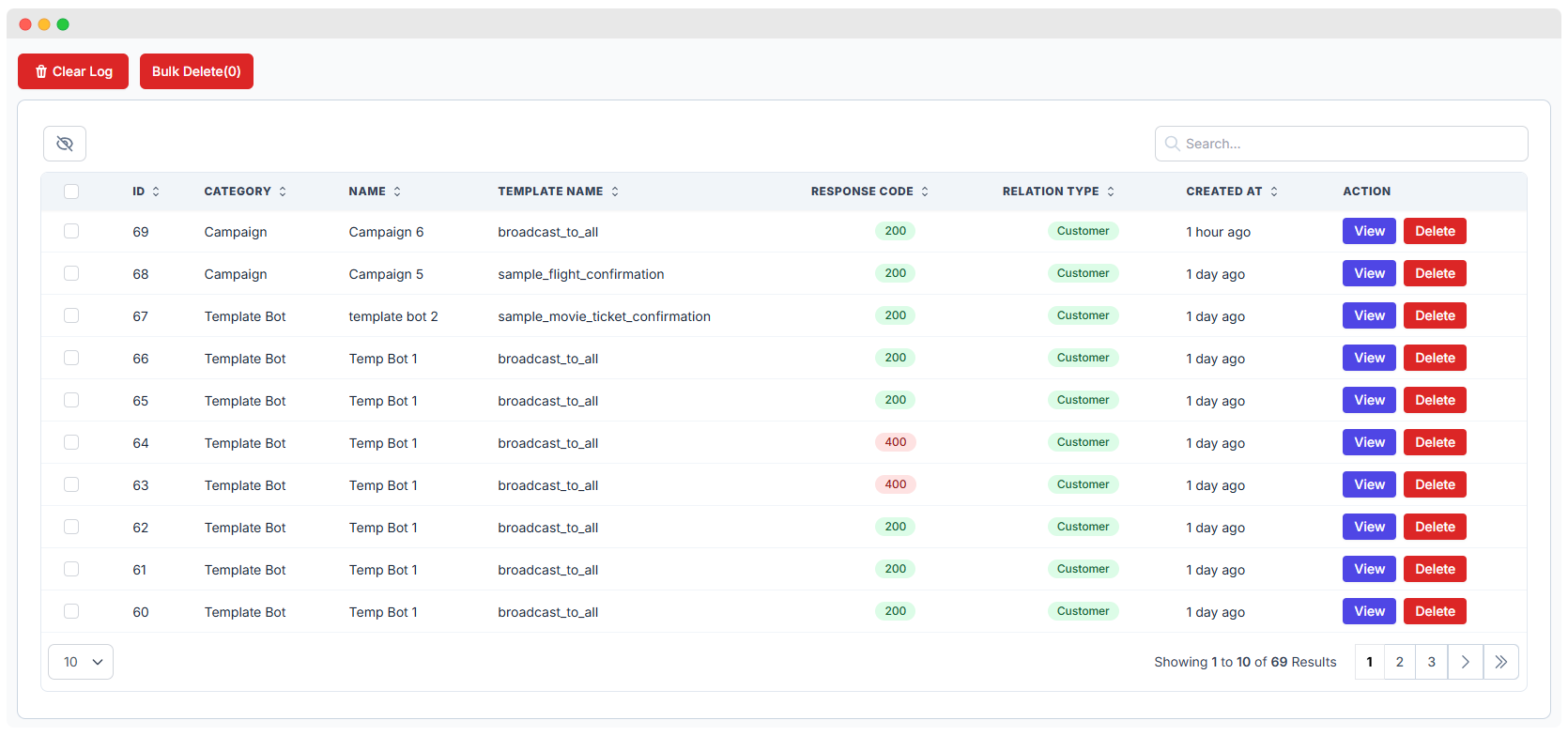
Activity Log Table
-
Activity Log Table Columns
: What you see
- • ID : Unique identifier for each log entry
- • Date : When the action occurred
- • User : Who performed the action (staff member or system)
- • Action : What was done (e.g., Contact Created, Message Sent, Setting Updated)
- • Description : Additional details about the action
- • IP Address : The IP address from which the action was performed
- • Action : View detailed log entry
The table provides a clear, chronological view of all activities. Use sorting and filtering to find specific events.
Filtering and Searching Logs
-
Filtering and Searching
: Find specific logs
- • Date Range : Filter by specific date or date range
- • User : Filter by staff member to see their activity
- • Action Type : Filter by action category (e.g., Contact, Message, Settings)
- • Keyword Search : Search descriptions for specific terms
- • Export : Download filtered logs for external review
Filtering is essential for large activity logs. Narrow down results to find exactly what you're looking for.
Bulk Management
-
Bulk Management
: Actions on multiple logs
- • Select Multiple : Checkbox selection for batch operations
- • Bulk Delete : Remove multiple log entries at once (if permissions allow)
- • Bulk Export : Export selected logs to CSV or PDF
Bulk actions save time when managing large numbers of log entries. Use with caution to avoid accidental deletions.
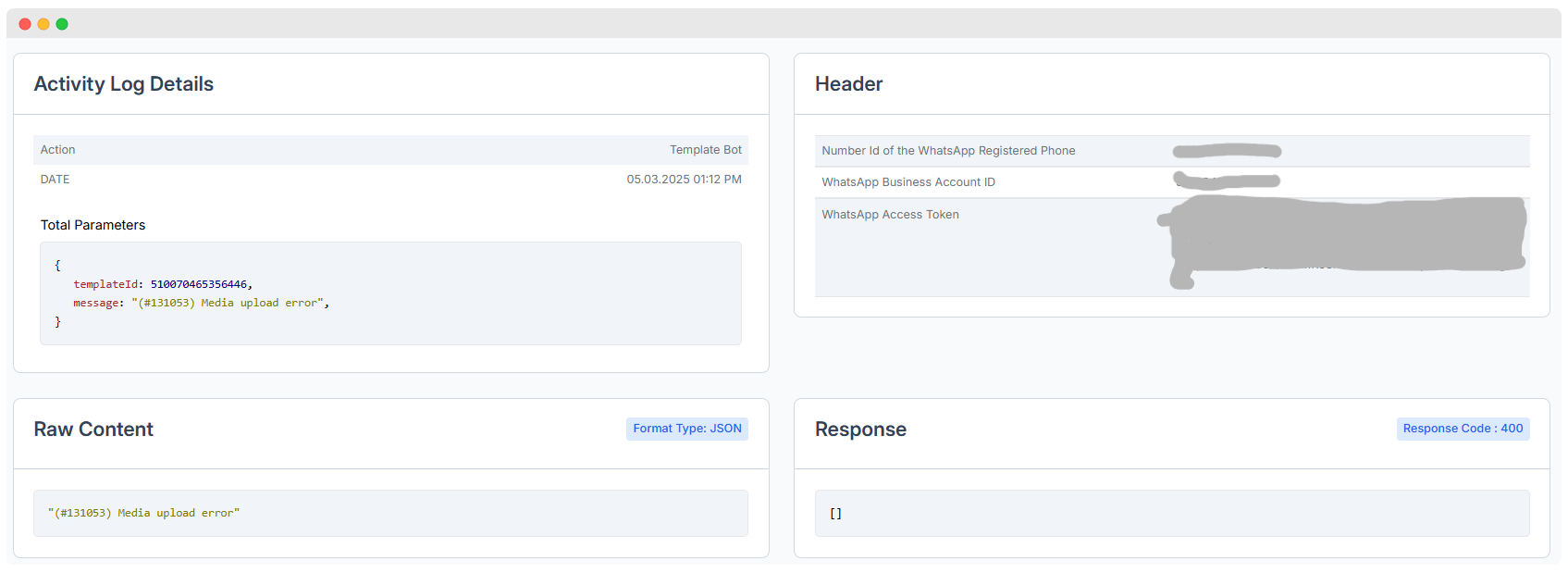
Viewing Detailed Log Entry
-
Viewing Detailed Log Entry
: Deep dive
- • Click View : From Action column to open detailed log modal
- • Full Context : See complete information including before/after values
- • Related Data : View associated contact, message, or setting
- • Timestamps : Precise time of action
- • User Info : Full user details including role and IP
Detailed views provide full context for each action, helping you understand exactly what happened and why.
Best Practices for Activity Log Management
-
Best Practices for Activity Log Management
: Tips
- • Review Regularly : Check logs periodically for unusual patterns
- • Set Retention Policy : Define how long logs should be kept
- • Restrict Access : Only admins or trusted staff should view logs
- • Export for Compliance : Regularly export logs for regulatory requirements
- • Monitor Critical Actions : Pay special attention to permission changes, deletions, bulk operations
- • Investigate Anomalies : Look into unexpected IP addresses or off-hours activity
